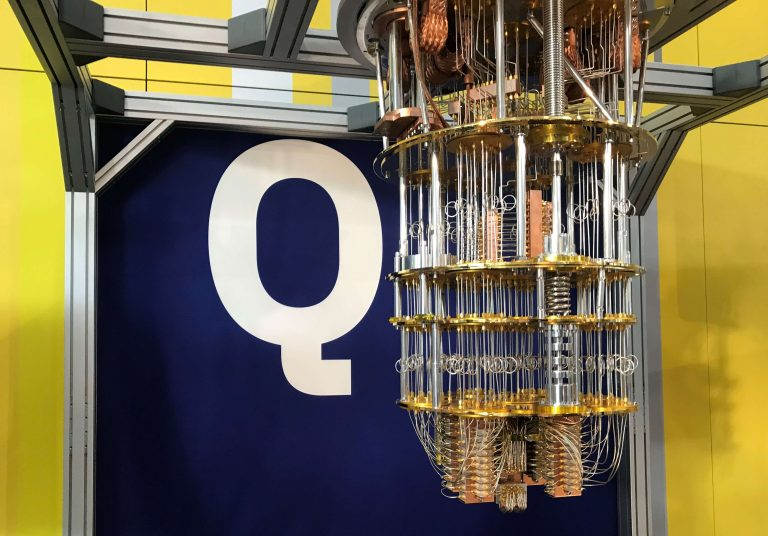
What is Quantum Computing?
From Wikipedia
"A quantum computer is a computer that exploits quantum mechanical phenomena. At small scales, physical matter exhibits properties of both particles and waves, and quantum computing leverages this behavior using specialized hardware. Classical physics cannot explain the operation of these quantum devices, and a scalable quantum computer could perform some calculations exponentially faster than any modern "classical" computer. In particular, a large-scale quantum computer could break widely used encryption schemes and aid physicists in performing physical simulations; however, the current state of the art is still largely experimental and impractical."
Preparing for post-quantum computing security involves understanding the risks associated with quantum computing, particularly its potential to break traditional encryption algorithms. Companies can take the following steps to prepare for post-quantum cryptography (PQC):
- Inventory and classify data: Review and classify your data to understand what needs stronger protection. Consider the data scraping threat, and ensure that sensitive data is safe now and in the future.
- Understand future exposure: Assess how your data is currently protected and whether it will be at risk once quantum computing arrives. Identify where cryptography is embedded in your systems and how data is being protected.
- Create a mitigation strategy: Develop mitigation groups and strategies, including a data security policy, incident response plan, and business recovery plan. Assess potential exposure of stored data and consider additional layers of encryption.
- Remain crypto-agile: As PQC standards change, ensure your infrastructure can adapt to new threats and technologies. Work on making your systems forward-compatible with new standards.
There are three main PQC implementation options to consider:
- Follow NIST's research and consider any algorithms it vets. Currently, four primary finalist algorithms remain uncracked and potentially viable, while three additional algorithms are also being studied for viability.
- Explore quantum key distribution (QKD), which uses quantum mechanics to securely exchange encryption keys. However, note that the National Security Agency has stated this option is not viable on its own as it now stands.
- Combine PQC encryption standards and QKD, making it more difficult for attackers to access data in transit, as they would need to break through both encryption and QKD.
AI is cool, but we have had models working for years. It will be disruptive for sure, but with Quantum computers training the AI, that is when stuff comes alive. Disruption like the world has never seen. That problems we can solve with Quantum for tech is simply amazing, Cure Cancer? Map finish mapping the genome?
Hang on, the ride is about to start.